That’s what the CEO of a small company asked the head of his information technology (IT) staff. On Shark Tank at Computerworld there was an article on February 21, 2020 titled Flashback Friday: They’re due someone’s undying gratitude.
His IT chief said it would be time consuming but not
impossible. Then he started calling each employee to ask for the password on
their company desktop computer - so IT could check it for ‘viruses and stuff.’ His
staff logged onto each of the seventy computers (as a remote desktop) and fished
around. It took them a day and a half to find every copy of that email and replace
it with a similar one.
What could have been worth all that trouble? The offending
email apparently had graphics about salaries, which had a highly confidential spreadsheet
embedded in them. That spreadsheet contained
a salary history for every employee in the company!
Back on June 12, 2012 at Think Outside the Slide Dave Paradi
had another article that discussed Solving problems caused by embedding. He pointed
out a PowerPoint Peril - that it was possible to accidentally link to and include
an Excel spreadsheet with such sensitive information when creating slides.
My wife told me she once heard of a similar situation. A
networked hard drive (Z) had been used to transfer files between departments in
a company. A department manager asked for salary info, and accounting put a
spreadsheet onto that Z drive. They emailed saying it had been sent. That
department manager then was supposed to delete it, just a few minutes after he had copied
it to his computer. He did not, and it stayed out on the Z drive for weeks –
where several other employees could have accessed it.
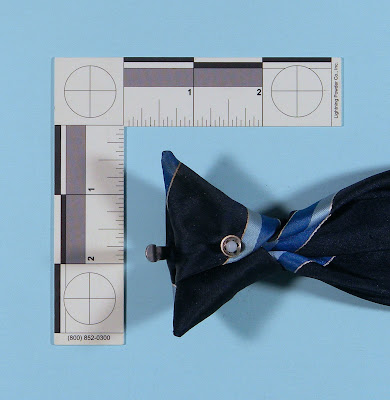
My father once told me about the analog equivalent which had happened way back in 1945. He then was a professor at the University of Cincinnati. The American Association of University Professors (AAUP) had asked the administration for salary information, and they said no darn way. But the administration had been recycling their carbon paper. Another curious young professor got a piece from a box he had picked up to use in his typewriter, and realized it only had been used once.
So he held it up to his office window where it was
illuminated by the afternoon sun. He saw tables of numbers and realized it was part
of the denied information. Then he grabbed another three boxes, which had the
rest of the payroll spreadsheet from their accounting machine. He passed it all
on to the AAUP. Of course he said don’t you dare tell anyone who you got this from.
After that discussions about raising salaries got much more interesting.
Images of fishing and carbon paper were modified from those found at Wikimedia Commons.
Images of fishing and carbon paper were modified from those found at Wikimedia Commons.